[Question] Setting up a bridged network for HomeAssistant in KVM Fedora
[Question] Setting up a bridged network for HomeAssistant in KVM Fedora
cross-posted from: https://mander.xyz/post/16531247
I have tried to follow several tutorial to setup using either
ipornmtui:
- https://linuxconfig.org/how-to-use-bridged-networking-with-libvirt-and-kvm
- https://www.redhat.com/sysadmin/setup-network-bridge-VM
However, the bridge inherits the MAC address of host after enslaving the host hardware
enp1s0.... This causes my router to give both the host and the bridge the same ip address, making the ha instance inaccessible.The red hat tutorial clearly show that the bridge and the host have different IP, so I was wondering if I am doing something wrong.
alternatively, I can set the home assistant vm to run in NAT and port forward from host, but I have several device that communicate over different ports. So it would be annoying to forward all these ports. Not to mention, many appliances don't have documentation about the ports they use.
I can also potentially use virtualbox, but it is not well supported on silverblue, especially with secureboot enabled.
[Question] Setting up a bridged network for HomeAssistant in KVM Fedora
[Question] Setting up a bridged network for HomeAssistant in KVM Fedora
I have tried to follow several tutorial to setup using either ip or nmtui:
- https://linuxconfig.org/how-to-use-bridged-networking-with-libvirt-and-kvm
- https://www.redhat.com/sysadmin/setup-network-bridge-VM
However, the bridge inherits the MAC address of host after enslaving the host hardware enp1s0.... This causes my router to give both the host and the bridge the same ip address, making the ha instance inaccessible.
The red hat tutorial clearly show that the bridge and the host have different IP, so I was wondering if I am doing something wrong.
alternatively, I can set the home assistant vm to run in NAT and port forward from host, but I have several devices that communicate over different ports. So it would be annoying to forward all these ports. Not to mention, many appliances don't have documentation about the ports they use.
I can also potentially use virtualbox, but it is not well supported on silverblue, especially with secureboot enabled.
The Worst Devices of CES 2024! By iFixIt
The Worst Devices of CES 2024! By iFixIt
Open link in next tab
Piped
https://www.youtube.com/watch?v=NXhmnQzZ7n8
An alternative privacy-friendly YouTube frontend which is efficient by design.

TIL Canadian Bacon is Not a Canadian Thing; Hawaiian Pizza, On The Other Hand, Is Invented in Canada.
TIL Canadian Bacon is Not a Canadian Thing; Hawaiian Pizza, On The Other Hand, Is Invented in Canada.
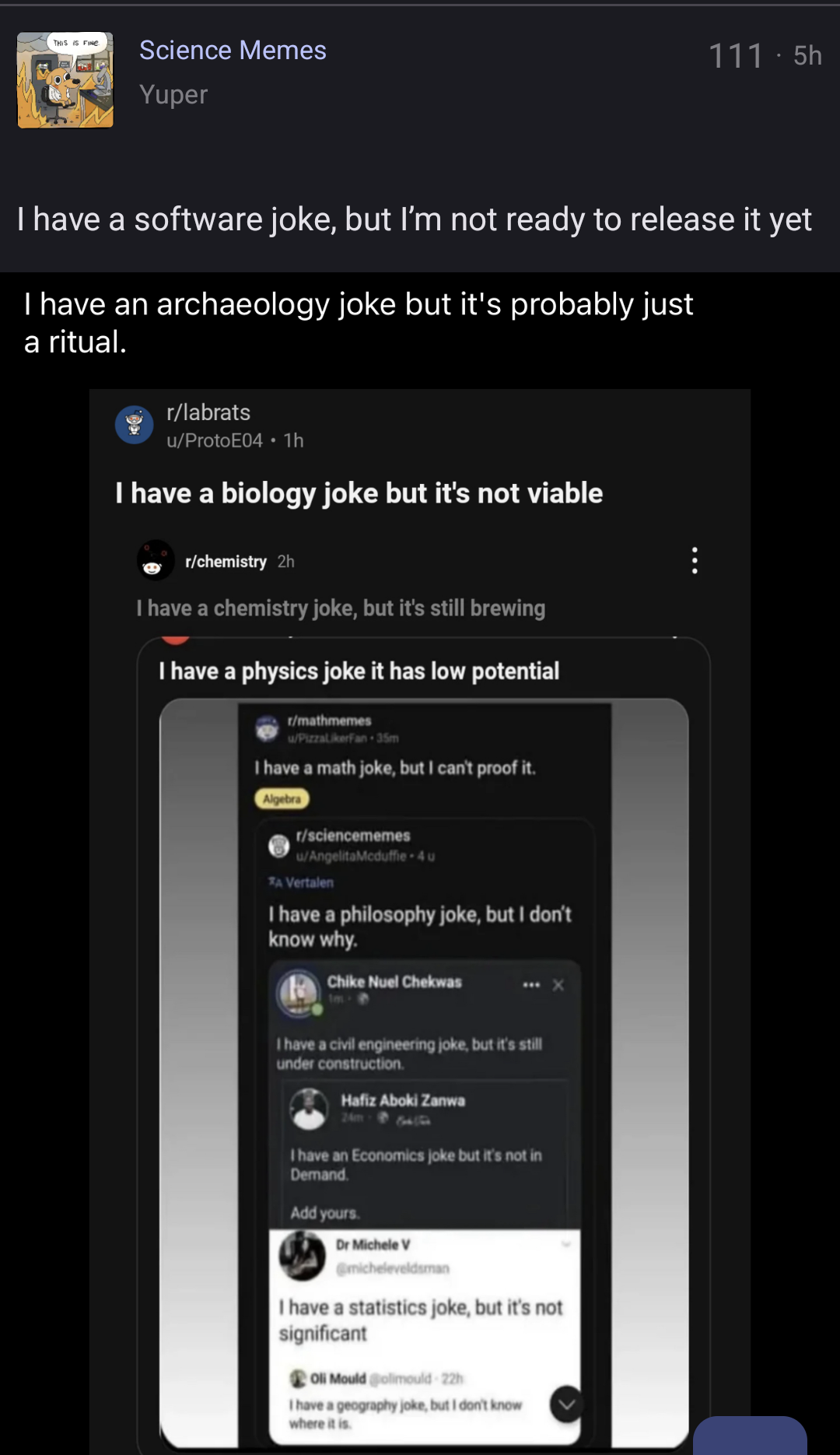
I have a logic joke, and it is inductively defined as follows: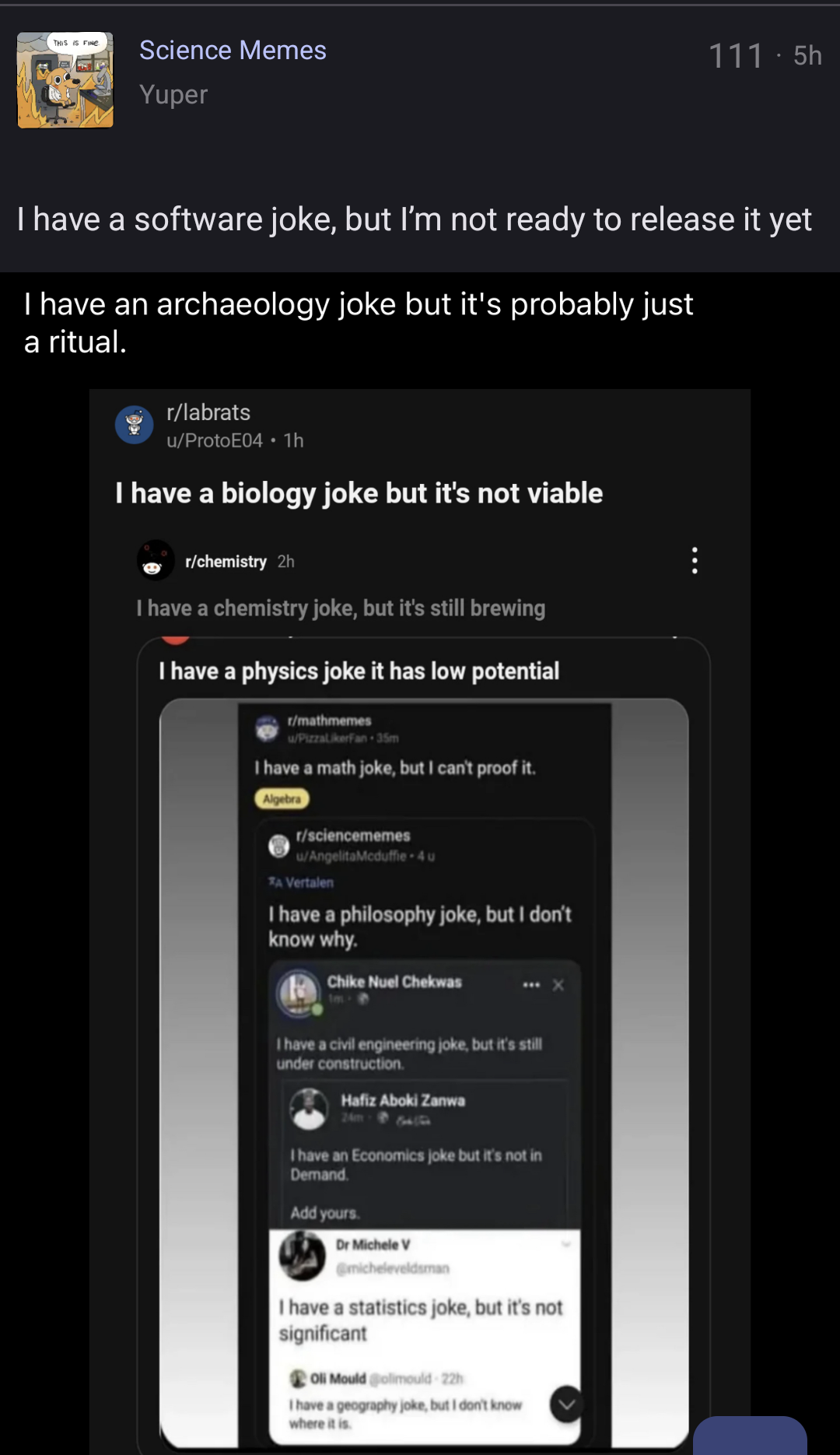
I have a logic joke, and it is inductively defined as follows:
Question About TPM Autodecrypt
Question About TPM Autodecrypt
I have setup my fedora to use LUKS encryoted partitions. But entering two passwords gets quite tiring, as I shutdown my laptop quite often to get the benefit of LUKS (I am assuming nothing is encrypted when in suspend, please correctme if I am wrong)
I am thinking about setting up TPM autodecrypt. However, I was wondering does the decryption happen on boot or after I login?
If it happens on boot, then it seems like the benefit is pretty limited compare to a unencrypted drive. Since the attacker can simply boot my laptop and get the unecrypted drive.
Am I missing something here? I was wondering is there a way for me to enter my password once and unlock everything, from disk to gnome keyring?
Does Graphene OS have FRP when no google account was added?
Does Graphene OS have FRP when no google account was added?
Just a curiosity. Theoretically FRP (factory reset protection) can use the current login password as a way of authentication after reset. But everything on the web states that you will need a Google account to take advantage of he feature.
Fairphone 5 Released
Fairphone 5 Released
Open link in next tab
Fairphone 5 | Fairphone
https://shop.fairphone.com/fairphone-5
Designed for you. Made Fair. Discover the newest member of the Fairphone family.



