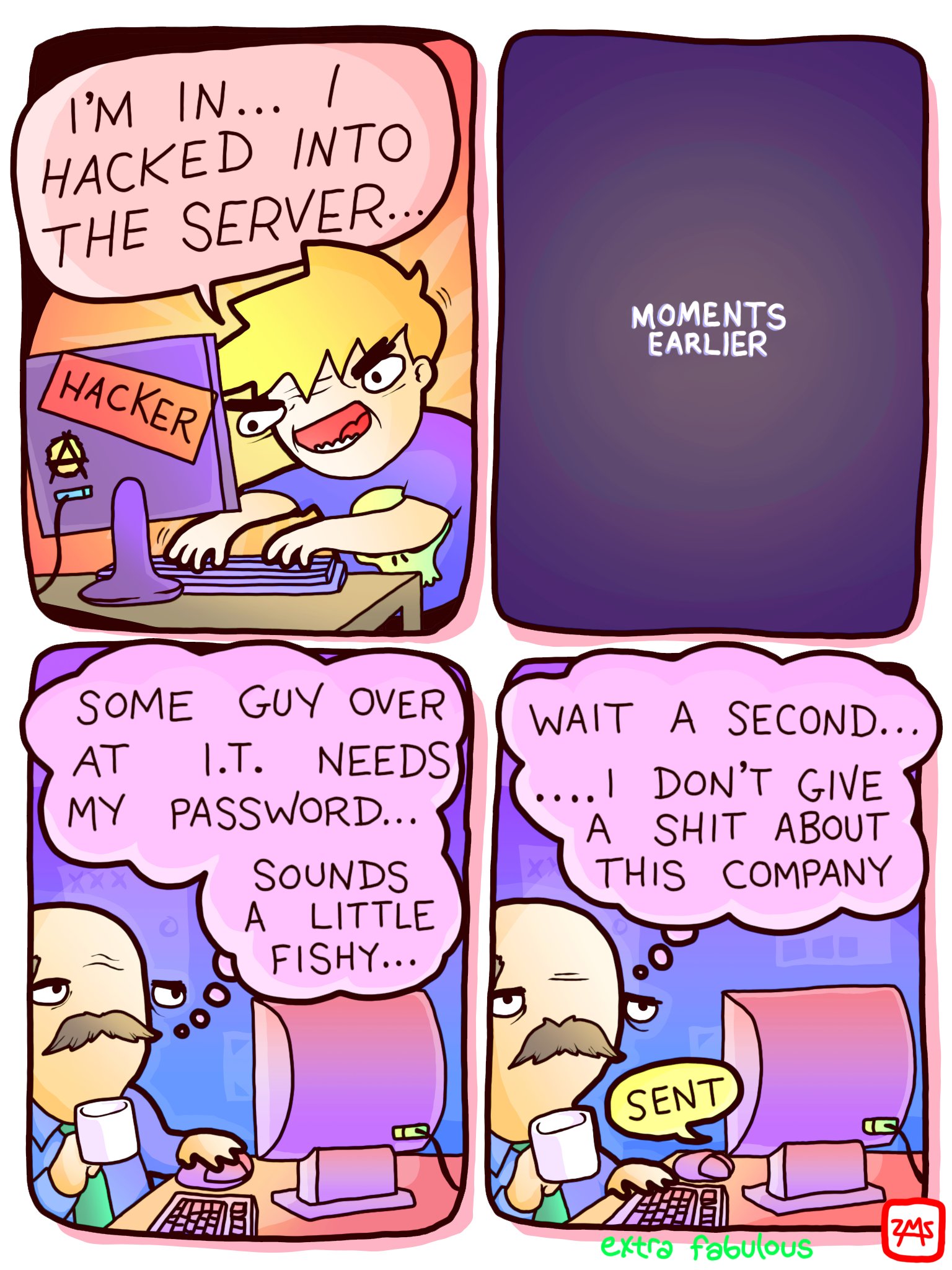
A lot of hacking is actually social engineering. It's not hard to get a tech-illiterate person to give up their password, and that's the softest target for an attack.
Nowadays you'd probably be more likely to get a hit by putting an "Anime titties" label on the drive
Just put the CEO's name on it and a very recent date. They'll be dying to know what secret information the CEO was carrying around.
I prefer a label that says, "Warning: USB stick contains scary virus. Do not plug into a computer"
There are usb sticks that can kill your pc by getting charged and then discharging all the electricity at once to your pc so no sandbox will save you in situations like those.
Me: Plugs USB into throwaway computer. Computer: dies. Me: "well that's a pretty boring virus!"
Or even jaded tech savvy people. I work in IT and there have been a number of times that I have witnessed or heard about people who know better causing an incident because they're burnt out or irate.
Hacker voice: "I'm in"
Looks at overly complicated industry software he's never even heard of before
"I'm out"
Wait, I have an idea! Yes, just as I thought, I can overlay their proprietary operating system with this fancy looking graphical interface that resembles nothing and gain full control of their system. I'm back in!
I was thinking of the James Bond movies where they show hacking to be a guy wearing glasses looking for a glowing ball in a flashing GUI that he rotates around somehow by typing really fast.
So they have a fancy representation of ... something with a hex table, that then transforms into a map of London given the right key?
We have these obligatory online seminars about web security /privacy at work.
Turns out that for some reason, with Privacy Badger enabled, they appear as "passed" instantly. I never saw a single second of these endless seminars.
I tried to tell the IT guy but he couldn't care less and I suspect he didn't even know what Privacy Badger actually is
Or maybe he feels that these seminars are for people who don't use things like privacy badger.
(Opens DOS, frantically types)
“Heh. I was able to SSH right into their jpg with nothing but an Ethernet cable and router grease.”
We get fake phishing emails that are actually from IT and if we don't recognize and report them, we get a talking-to. It's a good way of keeping employees vigilant.
A friend (who actually works in IT) apparently has a good system at his company. It actually automates turning real phishing attempts into internal tests. It effectively replaces links etc and sends it onwards. If the user actually clicks through, their account is immediately locked. It requires them to contact IT to unlock it again, often accompanied by additional training.
Wait. So your friend's company has the ability to reliably detect phishing attacks, but instead of just blocking them outright, it replaces the malicious phishing links with their own phishing links, sends those on to employees, and prevents them from doing their jobs of they fall for it?
Sounds like your friend's company's IT people are kind of dickheads
I work at a company that does something similar; it can be annoying to deal with these fake phishing emails from our own IT, but a 10-15 minute training session if you fail is a lot less disruptive than what can happen if you clicked the real link instead.
I consider myself a bit more tech-savvy than average, but I’ve almost fallen for a couple of these fake phishing emails. It helps me to keep up with what the latest versions of these attacks look like (and keeps me on my toes too…)
It's not every phishing email. I think it's technically those that get through the initial filters, and get reported, but don't quote me on that. Apparently it's quite effective. They also don't need to report every one. It's only if they do something that could have compromised the company that causes a lock down. It's designed to be disruptive and embarrassing, but only if they actively screw up.
Well the company probably can't detect them reliably, so wih the ones it does detect it trains them to avoid the ones that they can't detect.
My last company did this. They'd also send out surveys and training from addresses I didn't recognize, so I'd report those, too, only to be told they were legit 😂
Yeah this is a running joke at our workplace too. Only to be asked by some manager to do those week or few later
For me (us) it's simply because the security training emails are sent from some 3rd party service with sender email like fuckme-security@asshole.ml
I send supervisor emails about stuff I'm not gonna do to my spam folder as well.....
"Did you get the email?"
"Nope, sorry, it looked a little suspicious so I didn't open and sent it to spam.."
Basically you created a echo chamber at work where you can only hear what you want to hear
I just realised how you control reality at work and how much enjoyment you get.... Until you are enjoying too much and get fired
My workplace does this too. I can usually tell when the email isn't a legit phishing email but an IT test though. Not sure how helpful that is.
We get those, but the sender email shows up as blahblah@employersname.kn0wbe4.compromisedblog.org or whatever. Literally the most obvious possible address. I'm always tempted to forward one to IT and ask if they're serious with that shit.
Ours are the opposite: the sender's email shows up as a normal name@company.com email. Gmail is supposed to warn when a return address is being spoofed like that, but I guess my company turned that warning off for these fake phishing emails. There's still no SPF but I don't check the SPF unless an email looks suspicious so I hope that that warning will work for real, sophisticated phishing.
No it isn't.
Consider third-party vendor employees who have accounts at your workplace. They don't know what the norms are, or the safe URLs. Half your employees in non-coding roles don't know what the safe URLs are either. There's so much internal SSO mess that just about anything could be a real redirect. Overengineered internal messy networks keep any of this from actually accomplishing its intended purpose of "teaching employees a lesson".
I'm not sure what's worse: that you're teaching them to click on whatever they want because it's impossible to tell the difference, or that you're teaching them to click on nothing, which probably keeps them from doing their jobs.
Stop using email entirely and half of this goes away. Just tell them not to plug in USB drives.
I always just ignore anything that looks dodgy, I can't be bothered to spend the time reporting emails when I get so damn many that are either spam or phishing
Duo push more like duo push you off a cliff because you forgot to do your Spanish lessom
I’m all for acting your wage, but I don’t want to make victims of anyone who is interacting with my company simply because I was feeling spiteful. The company will be fine, the tons of people who just had their information leaked are the ones who are truly inconvenienced and may face financial repercussions later on when their information is distributed. Just something to consider
A good portion of the movie Hackers was social engineering. That's how Mitnick got into a lot of systems as well. Why search for vulnerabilities in apps when people are much easier to manipulate.
As somone in IT who has to deal with executives I can assure you that high compensation has no correlation with good security practices :(