Real gaming router
Real gaming router
Open link in next tab
Real gaming router
https://kittenlabs.de/real-gaming-router/
Running GTA: Vice City on a TP-Link TL-WDR4900 wireless router
Cracking Meta’s Messenger Certificate Pinning on macOS
Cracking Meta’s Messenger Certificate Pinning on macOS
Open link in next tab
Cracking Meta’s Messenger Certificate Pinning on macOS
https://texts.blog/2024/02/20/cracking-metas-messenger-certificate-pinning-on-macos/
Bypassing certificate pinning in Meta’s Messenger application on macOS.
World Server Throwing Championship
World Server Throwing Championship
Open link in next tab
World Server Throwing Championship
https://www.cloudfest.com/world-server-throwing-championship
The World Server Throwing Championship at CloudFest lets Cloud professionals demonstrate their raw power! Are you strong enough?

Ramrecovery: Simple demo illustrating remanence of data in RAM (see Cold boot attack) using a Raspberry Pi
Ramrecovery: Simple demo illustrating remanence of data in RAM (see Cold boot attack) using a Raspberry Pi
Open link in next tab
GitHub - anfractuosity/ramrecovery: Simple demo illustrating remanence of data in RAM (see Cold boot attack) using a Raspberry Pi. Loads many images of the Mona Lisa into RAM and recovers after powering off/on again.
https://github.com/anfractuosity/ramrecovery
Simple demo illustrating remanence of data in RAM (see Cold boot attack) using a Raspberry Pi. Loads many images of the Mona Lisa into RAM and recovers after powering off/on again. - anfractuosity...
DEF CON 30 - Sam Bent - Tor - Darknet Opsec By a Veteran Darknet Vendor
DEF CON 30 - Sam Bent - Tor - Darknet Opsec By a Veteran Darknet Vendor
Open link in next tab
DEF CON 30 - Sam Bent - Tor - Darknet Opsec By a Veteran Darknet Vendor
https://www.youtube.com/watch?v=01oeaBb85Xc
The hacking subculture's closest relative is that of the Darknet. Both have knowledgeable people, many of whom are highly proficient with technology and wish...
Interesting double-poly latches inside AMD's vintage LANCE Ethernet chip
Interesting double-poly latches inside AMD's vintage LANCE Ethernet chip
Open link in next tab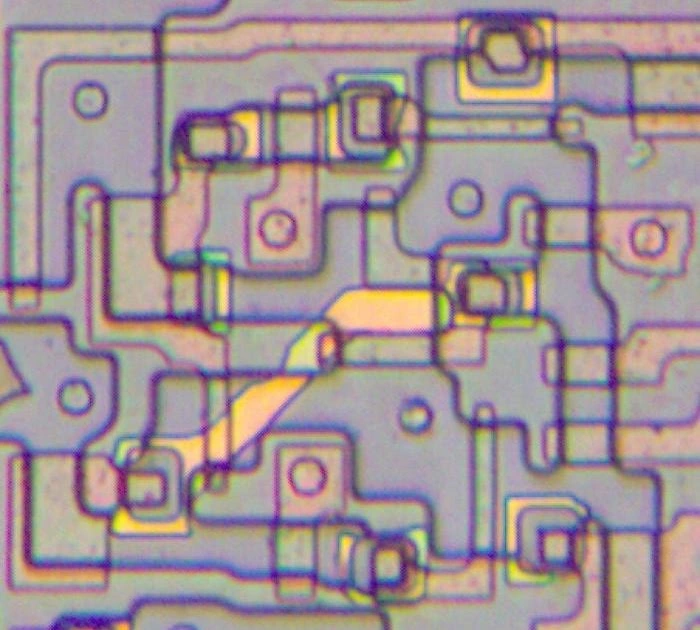
Interesting double-poly latches inside AMD's vintage LANCE Ethernet chip
https://www.righto.com/2023/12/amd-lance-ethernet-double-poly.html
I've studied a lot of chips from the 1970s and 1980s, so I usually know what to expect. But an Ethernet chip from 1982 had something new: a ...
[37C3] There oughta be a Game Boy capture cartridge.
[37C3] There oughta be a Game Boy capture cartridge.
Open link in next tab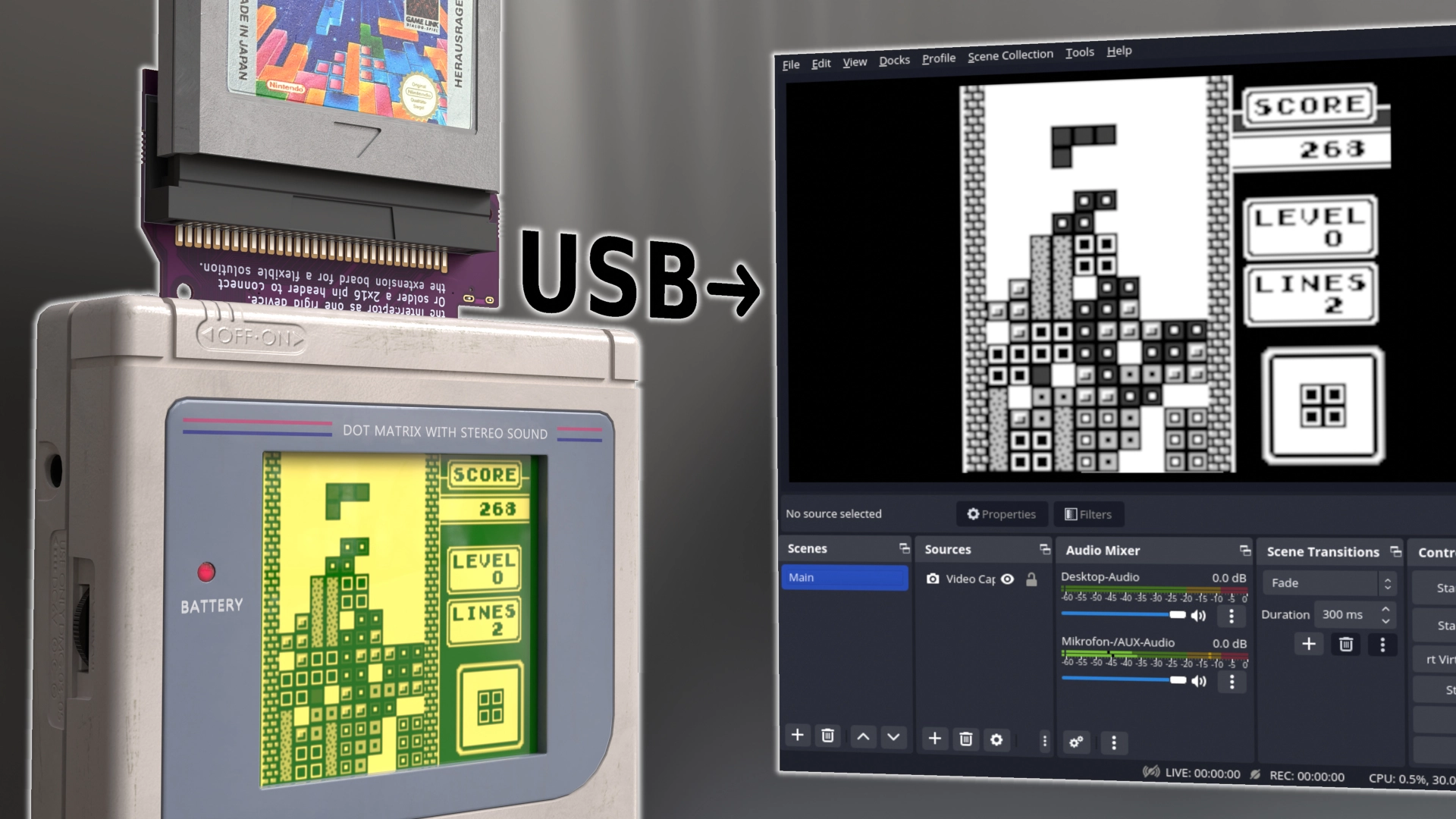
There oughta be a Game Boy capture cartridge.
https://there.oughta.be/a/game-boy-capture-cartridge
I present to you: The GB Interceptor. It is an adapter that goes between an unmodified Game Boy and the cartridge and offers a video stream of the game via USB. Click the image to see the video on youtube.com. The video above should give you a good overview of what it does, how it works and what its limitations are. This article here goes more into the technical details of how it works. If you are interested in how to order and build your own GB Interceptor, check out github and the order and build video.
[37C3] Emulating an iPod Touch 1G and iPhoneOS 1.0 using QEMU (Part I) | Martijn de Vos
[37C3] Emulating an iPod Touch 1G and iPhoneOS 1.0 using QEMU (Part I) | Martijn de Vos
Open link in next tab
Emulating an iPod Touch 1G and iPhoneOS 1.0 using QEMU (Part I) | Martijn de Vos
https://devos50.github.io/blog/2022/ipod-touch-qemu/
My personal website.
[37C3] Red Team vs. Blue Team: A Real-World Hardware Trojan Detection Case Study Across Four Modern CMOS Technology Generations
[37C3] Red Team vs. Blue Team: A Real-World Hardware Trojan Detection Case Study Across Four Modern CMOS Technology Generations
Open link in next tab
Red Team vs. Blue Team: A Real-World Hardware Trojan Detection Case Study Across Four Modern CMOS Technology Generations
https://eprint.iacr.org/2022/1720
Verifying the absence of maliciously inserted Trojans in ICs is a crucial task – especially for security-enabled products. Depending on the concrete threat model, different techniques can be applied for this purpose. Assuming that the original IC layout is benign and free of backdoors, the primary security threats are usually identified as the outsourced manufacturing and transportation. To ensure the absence of Trojans in commissioned chips, one straightforward solution is to compare the received semiconductor devices to the design files that were initially submitted to the foundry. Clearly, conducting such a comparison requires advanced laboratory equipment and qualified experts. Nevertheless, the fundamental techniques to detect Trojans which require evident changes to the silicon layout are nowadays well-understood. Despite this, there is a glaring lack of public case studies describing the process in its entirety while making the underlying datasets publicly available. In this work, we aim to improve upon this state of the art by presenting a public and open hardware Trojan detection case study based on four different digital ICs using a Red Team vs. Blue Team approach. Hereby, the Red Team creates small changes acting as surrogates for inserted Trojans in the layouts of 90 nm, 65 nm, 40 nm, and 28 nm ICs. The quest of the Blue Team is to detect all differences between digital layout and manufactured device by means of a GDSII–vs–SEM-image comparison. Can the Blue Team perform this task efficiently? Our results spark optimism for the Trojan seekers and answer common questions about the efficiency of such techniques for relevant IC sizes. Further, they allow to draw conclusions about the impact of technology scaling on the detection performance.